recent这个模块很有趣,善加利用可充分保证您服务器安全。
设定常用参数:
--name #设定列表名称,默认DEFAULT。
--rsource #源地址,此为默认。
--rdest #目的地址
--seconds #指定时间内
--hitcount #命中次数
--set #将地址添加进列表,并更新信息,包含地址加入的时间戳。
--rcheck #检查地址是否在列表,以第一个匹配开始计算时间。
--update #和rcheck类似,以最后一个匹配计算时间。
--remove #在列表里删除相应地址,后跟列表名称及地址。示例:
1.限制80端口60秒内每个IP只能发起10个新连接,超过记录日记及丢失数据包,可防CC及非伪造IP的syn flood。
iptables -A INPUT -p tcp --dport 80 --syn -m recent --name webpool --rcheck --seconds 60 --hitcount 10 -j LOG --log-prefix 'DDOS:' --log-ip-options
iptables -A INPUT -p tcp --dport 80 --syn -m recent --name webpool --rcheck --seconds 60 --hitcount 10 -j DROP
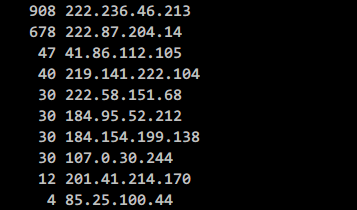
iptables -A INPUT -p tcp --dport 80 --syn -m recent --name webpool --set -j ACCEPT备忘:每个IP目标端口为80的新连接会记录在案,可在/proc/net/xt_recent/目录内查看,rcheck检查此IP是否在案及请求次数,如果超过规则就丢弃数据包,否则进入下条规则并更新列表信息。
2.发送特定指定执行相应操作,按上例如果自己IP被阻止了,可设置解锁哦。
iptables -A INPUT -p tcp --dport 5000 --syn -j LOG --log-prefix "WEBOPEN: "
#记录日志,前缀WEBOPEN:
iptables -A INPUT -p tcp --dport 5000 --syn -m recent --remove --name webpool --rsource -j REJECT --reject-with tcp-reset
#符合规则即删除webpool列表内的本IP记录3.芝麻开门,默认封闭SSH端口,为您的SSH服务器设置开门暗语。
iptables -A INPUT -p tcp --dport 50001 --syn -j LOG --log-prefix "SSHOPEN: "
#记录日志,前缀SSHOPEN:
iptables -A INPUT -p tcp --dport 50001 --syn -m recent --set --name sshopen --rsource -j REJECT --reject-with tcp-reset
#目标端口tcp50001的新数据设定列表为sshopen返回TCP重置,并记录源地址。
iptables -A INPUT -p tcp --dport 22 --syn -m recent --rcheck --seconds 15 --name sshopen --rsource -j ACCEPT
#开启SSH端口,15秒内允许记录的源地址登录SSH。
nc host 50001 #开门钥匙
telnet host 50001
nmap -sS host 50001指定端口容易被破解密钥,可以使用ping指定数据包大小为开门钥匙。
iptables -A INPUT -p icmp --icmp-type 8 -m length --length 78 -j LOG --log-prefix "SSHOPEN: "
#记录日志,前缀SSHOPEN:
iptables -A INPUT -p icmp --icmp-type 8 -m length --length 78 -m recent --set --name sshopen --rsource -j ACCEPT
#指定数据包78字节,包含IP头部20字节(ipv6为40字节),ICMP头部都是8字节,ping时指定数据大小50
iptables -A INPUT -p tcp --dport 22 --syn -m recent --rcheck --seconds 15 --name sshopen --rsource -j ACCEPT
#ipv4+28 ipv6+48
ping -s 50 host #Linux下解锁
ping -l 50 host #Windows下解锁