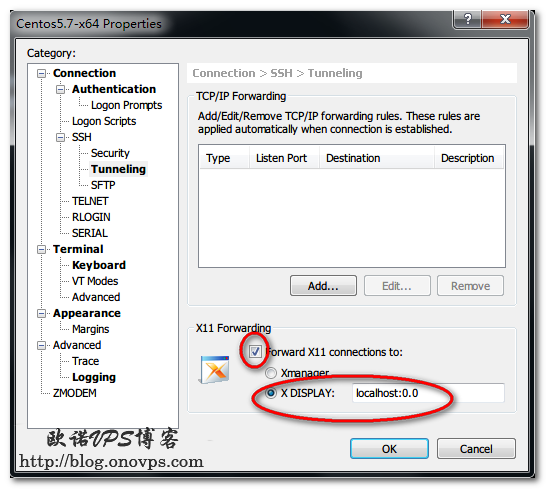
Centos安装X window配置ssh X转发
发布时间:July 14, 2012 // 分类:Linux基础 // No Comments
Linux下使用mutt、fetchmail、msmtp、procmail收取管理邮件
发布时间:July 14, 2012 // 分类:Mail // No Comments
这几个软件分工如下:
mutt:用户客户端MTA,用于邮件管理
fetchmai:连接邮件服务器收取邮件
msmtp:通过smtp协议发送邮件
procmail:邮件投递代理MDA,用于邮件投递或邮件过滤
安装:
#https://www.haiyun.me
yum install mutt fetchmail procmail
wget http://sourceforge.net/projects/msmtp/files/msmtp/1.4.28/msmtp-1.4.28.tar.bz2/download
tar jxvf msmtp-1.4.28.tar.bz2
cd msmtp-1.4.28
./configure --prefix=/usr/local/msmtp
make
make installmutt配置:
cat ~/.muttrc
set sendmail="/usr/local/msmtp/bin/msmtp" #MTA
set use_from
set reverse_name=yes
set editor="vim" #邮件编辑器
set folder = "/root/Mail" #邮件目录
set mbox_type = Maildir #邮件目录类型
set spoolfile = "/root/Mail/inbox" #收件箱
set move=yes #移动已读邮件
set mbox=~/Mail/seen #放已读邮件
set record=~/Mail/sent #放已发邮件
set postponed=~/Mail/draft #放草稿
set include #回复调用原文
auto_view text/html #自动显示html
set charset="utf-8" #编码默认mutt查看html邮件以htmlview显示乱码,配置为以w3m查看:
yum install w3m
cat ~/.mailcap
text/html ; w3m -T text/html -I %{charset} -dump %s ;nametemplate=%s.html ; copiousoutputfetchmail配置:
cat ~/.fetchmailrc
set logfile /var/log/fetchmail.log
poll smtp.www.haiyun.me
proto pop3
port 995
user 'user'
password 'passwd'
mda "/usr/bin/procmail -f %F -d %T";
ssl
keep
set daemon 60msmtp配置:
cat ~/.msmtprc
logfile /var/log/msmtp.log
account default
host smtp.www.haiyun.me
port 587
from admin@www.haiyun.me
auth login
tls on
tls_certcheck off
user user
password passwdprocmail配置:
cat ~/.procmailrc
PATH=/bin:/sbin:/usr/bin:/usr/sbin/:/usr/local/bin:/usr/local/sbin
MAILDIR=$HOME/Mail
DEFAULT=$MAILDIR/inbox
VERBOSE=off
LOGFILE=/var/log/procmaillog
:0
* .*
inbox分类
- Apache (13)
- Nginx (45)
- PHP (86)
- IIS (8)
- Mail (17)
- DNS (16)
- Cacti (14)
- Squid (5)
- Nagios (4)
- Puppet (7)
- CentOS (13)
- Iptables (23)
- RADIUS (3)
- OpenWrt (41)
- DD-WRT (1)
- VMware (9)
- 网站程序 (2)
- 备份存储 (11)
- 常用软件 (20)
- 日记分析 (10)
- Linux基础 (18)
- 欧诺代理 (0)
- Linux服务 (18)
- 系统监控 (4)
- 流量监控 (7)
- 虚拟化 (28)
- 伪静态 (2)
- LVM (3)
- Shell (18)
- 高可用 (2)
- 数据库 (16)
- FreeBSD (3)
- 网络安全 (25)
- Windows (35)
- 网络工具 (22)
- 控制面板 (3)
- 系统调优 (10)
- Cisco (3)
- VPN (6)
- ROS (20)
- Vim (14)
- KMS (4)
- PXE (2)
- Mac (1)
- Git (1)
- PE (1)
- LNS (2)
- Xshell (7)
- Firefox (13)
- Cygwin (4)
- OpenSSL (9)
- Sandboxie (3)
- StrokesPlus (1)
- AutoHotKey (4)
- Total Commander (3)
- WordPress (3)
- iMacros (6)
- Typecho (2)
- Ollydbg (1)
- Photoshop (1)
- 正则 (3)
- Debian (3)
- Python (8)
- NoSQL (6)
- 消息队列 (4)
- JS (7)
- Tmux (3)
- GO (7)
- HHVM (2)
- 算法 (1)
- Docker (2)
- PT (15)
- N1 (16)
- K2P (6)
- LUKS (4)
最新文章
- TEWA-1100G光猫使用
- 烽火光猫HG5382A3使用
- 记联通更换移动XG-040G-MD光猫
- smokeping slave同步错误illegal attempt to update using time解决
- 使用valgrind定位解决smartdns内存泄露
- 此内容被密码保护
- debian12下initramfs-tools配置ip子网掩码255.255.255.255/32失败解决
- iPhone查看屏幕供应商
- 光猫拨号ImmortalWrt/OpenWRT路由获取ipv6遇到的问题
- php-fpm错误error_log日志配置
最近回复
- opnfense: 谢谢博主!!!解决问题了!!!我之前一直以为内置的odhcp6就是唯一管理ipv6的方式
- liyk: 这个方法获取的IPv6大概20分钟之后就会失效,默认路由先消失,然后Global IPV6再消失
- 海运: 不好意思,没有。
- zongboa: 您好,請問一下有immortalwrt設定guest Wi-Fi的GUI教學嗎?感謝您。
- 海运: 恩山有很多。
- swsend: 大佬可以分享一下固件吗,谢谢。
- Jimmy: 方法一 nghtp3步骤需要改成如下才能编译成功: git clone https://git...
- 海运: 地址格式和udpxy一样,udpxy和msd_lite能用这个就能用。
- 1: 怎么用 编译后的程序在家里路由器内任意一台设备上运行就可以吗?比如笔记本电脑 m参数是笔记本的...
- 孤狼: ups_status_set: seems that UPS [BK650M2-CH] is ...
归档
- March 2025
- February 2025
- August 2024
- May 2024
- February 2024
- January 2024
- December 2023
- November 2023
- October 2023
- September 2023
- August 2023
- May 2023
- April 2023
- February 2023
- January 2023
- December 2022
- September 2022
- July 2022
- April 2022
- March 2022
- February 2022
- January 2022
- December 2021
- November 2021
- April 2021
- March 2021
- February 2021
- January 2021
- December 2020
- November 2020
- October 2020
- September 2020
- July 2020
- May 2020
- April 2020
- March 2020
- February 2020
- January 2020
- December 2019
- November 2019
- July 2019
- April 2019
- March 2019
- February 2019
- January 2019
- December 2018
- November 2018
- October 2018
- September 2018
- August 2018
- July 2018
- June 2018
- April 2018
- March 2018
- February 2018
- January 2018
- December 2017
- October 2017
- September 2017
- August 2017
- July 2017
- April 2017
- March 2017
- February 2017
- January 2017
- December 2016
- November 2016
- July 2016
- June 2016
- November 2015
- October 2015
- September 2015
- August 2015
- July 2015
- June 2015
- May 2015
- April 2015
- March 2015
- February 2015
- January 2015
- December 2014
- November 2014
- October 2014
- September 2014
- August 2014
- July 2014
- June 2014
- May 2014
- April 2014
- March 2014
- February 2014
- January 2014
- December 2013
- November 2013
- October 2013
- August 2013
- July 2013
- June 2013
- May 2013
- April 2013
- March 2013
- February 2013
- January 2013
- December 2012
- November 2012
- October 2012
- September 2012
- August 2012
- July 2012
- June 2012
- May 2012
- April 2012
- March 2012
- February 2012
- October 2011
- September 2011
- August 2011
- July 2011